Could your cloud be deleted?
Are a username and password all that stand between you and total loss?
Is your organisation’s IT health solely dependent on another company’s financial health?
As part of deciding to embrace cloud services, you must be able to identify a new set of risks to business continuity that perhaps weren’t a concern previously. Here’s just two…
You’ve decided to outsource your application to a SaaS (Software as a Service) or other public cloud provider. In large scale SaaS contracts, considerable attention is rightly placed on Service Level Agreements (SLAs) to ensure the availability of the application to the business. But what happens when an SLA can’t protect you? Have you considered how your business may continue to function if your cloud service was withdrawn without notice, due to bankruptcy or other government intervention?
Could you survive without the application?
Do you have a mitigation strategy that allows you to continue the business function in another way, should the SaaS vendor be forced to cease trading? How long can you go without having that application available? Can you migrate to another provider? Do you have manual options?
Can you proceed when you’re not able to recover your most recent data?
When a business is forced to cease trading by authorities, it mostly comes as a surprise and there is no opportunity for you to retrieve your data. Do you have a strategy to survive if you are blocked from accessing your own data? Can you export your data on a regular basis and work with the most recent export? How often must you run this export for it to be effective?
Administrator access to the cloud provider
In public cloud offerings, an administrator logs on to their cloud control panel via the internet. From there, they have full control of life-and-death actions, such as deleting servers and deleting backups.
Is access to your entire compute “data centre” protected by only one password?
We all have bad days – to err is human, but to provide risk mitigation is sensible business. Users and experts alike can be fooled into divulging their authentication credentials, especially in this age of Advanced Persistent Threats and Spear Phishing. Protect your cloud control panel against such risks – think of it as having the ability to delete your entire data centre and backup archive in one regrettable step.
If your cloud administration panel is only protected by a single password, consider Identity Access Management (IAM) solutions provided for your cloud host’s control panel.
- Multiple roles with differing access levels for different administrator accounts. Why does someone with a finance job function need to be able to delete servers?
- Two factor authentication. It’s easy to steal a password from a human, but it’s extremely difficult to steal the other half of any two factor authentication, such as a physical or virtual token. Two factor authentication is the strongest control you have to prevent unauthorised access.
- Recovery options. Does your cloud provider offer “offline” recovery options, if an intruder or employee goes rogue? What options do they give you in a worst case scenario?
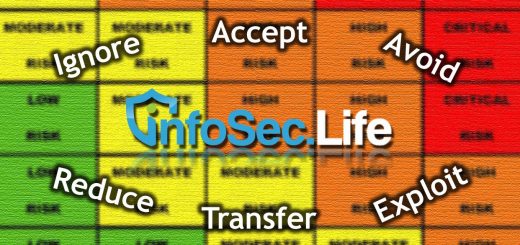
Ultimately, if the risk of accidental or malicious deletion is unpalatable regardless of controls, then perhaps public cloud is not a good match for your application. It is good to keep a realistic eye on your risks. But for everyone else, outsourcing services to the cloud is no different to any other business decision: risk assessments will help you understand your potential exposure, and what you can do about it.




Recent comments